NetSim Cyber: Model & Simulate Cyber Attack on Power Systems
Last updated: April, 2026
Modern electric power grids are no longer isolated physical systems. They are cyber-physical infrastructures where power equipment, communication networks, and control software operate together. While this convergence improves efficiency and automation, it also introduces cybersecurity risks.
The Threat is Real and Escalating
Power grids are now prime targets, surpassing other critical infrastructures in attack frequency. Three incidents illustrate:
The first confirmed cyber-induced blackout. Attackers remotely operated substations, cutting power to over 200,000 consumers.
Malware hard-coded for IEC-104 attempted physical destruction of substations during missile strikes - a clear cyber-kinetic attack.
State-sponsored actors covertly infiltrated U.S. power grid networks for months using legitimate admin tools, positioning for future disruption.
Why NetSim Cyber?
Improving Cyber Physical Power System (CPPS) security requires a realistic testbed that can replicate power-system behavior under malicious conditions.
Limitations of Hardware Testbeds
- High cost and procurement complexity
- Limited scalability - hard to replicate multi-substation scenarios
- Safety risks when running malicious attack scenarios
- Inflexible configurations - changes require physical rewiring
The Software Advantage
Software-based CPPS testbeds overcome these limitations and function as digital twins of real power systems. A complete CPPS testbed consists of:
- A power system simulator to model generators, power electronics, transmission, and distribution systems.
- A network simulator to model the underlying communication network and its cyber behavior.
NetSim Cyber provides the network simulation and attack-emulation layer required to complete this CPPS testbed.
NetSim Cyber - System Architecture
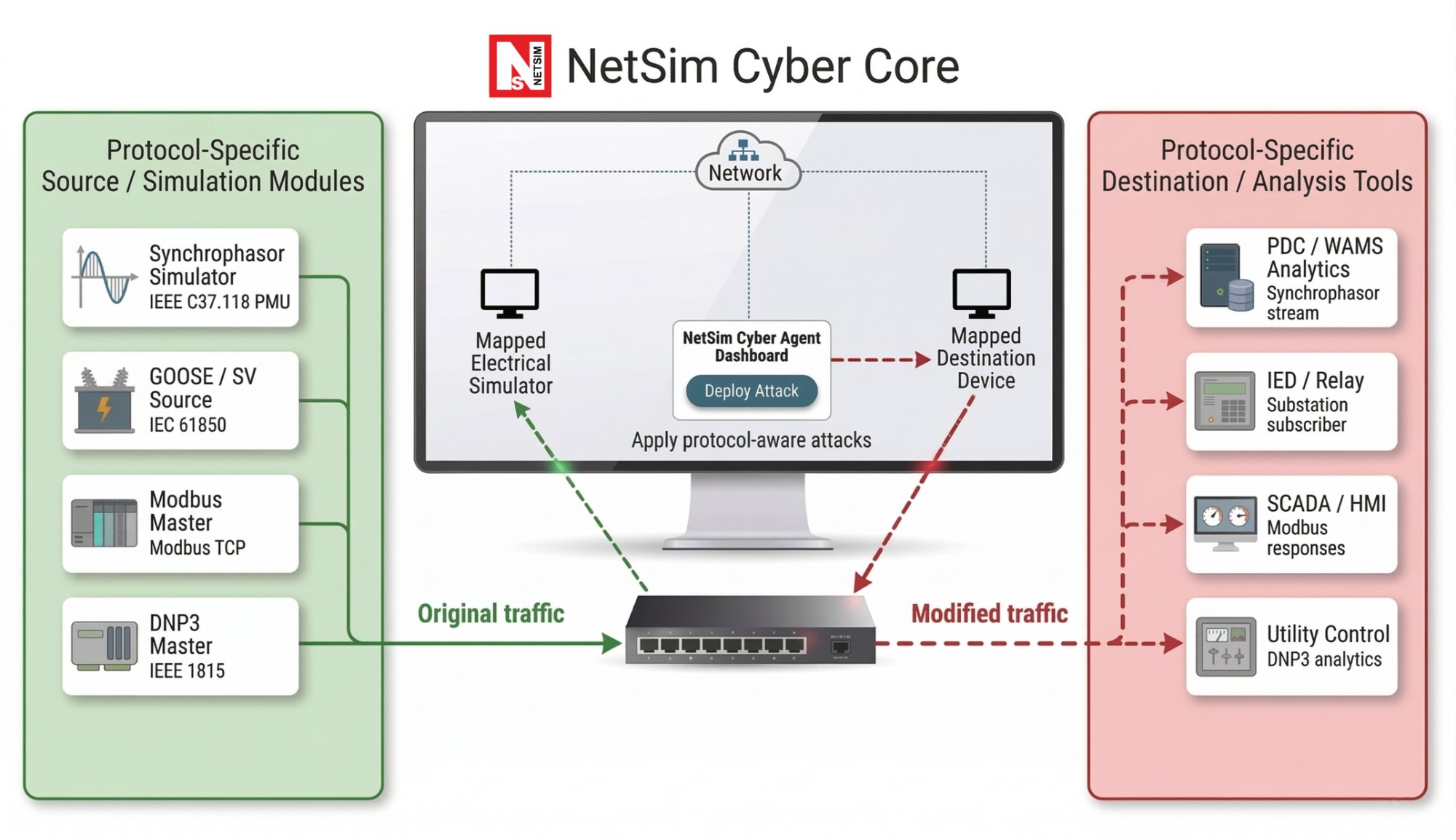
NetSim Cyber connects all protocol source simulators through a common NetSim Cyber Core that intercepts live traffic, applies protocol-aware attacks, recalculates checksums, and delivers wire-valid modified packets to destination analysis tools.
End-to-End CPPS Cyber Validation Workflow
The architecture operates across three systems over a controlled LAN-based test network:
- System 1 (Source): Protocol-specific simulators generate original traffic - Synchrophasor PMU, GOOSE/SV source, Modbus master, or DNP3 master.
- System 2 (NetSim Cyber Core): Intercepts traffic, applies protocol-aware attacks and recalculates checksums - modified packets remain indistinguishable on the wire.
- System 3 (Destination): Analysis tools receive and validate modified traffic - PDC/WAMS, IED/Relay, SCADA/HMI, or Utility Control.
Focused on Post-Exploitation Impact Analysis
Most cybersecurity tools ask: "How does an attacker get in?" NetSim Cyber asks a different question: “Once an attacker is inside, what damage can they do to the power grid?”
This distinction matters for critical infrastructure. A power utility cannot wait until after a breach to understand its consequences. By the time an attack is detected on a live grid, cascading failures may already be in motion. NetSim Cyber lets you study, measure, and prepare for attack impact in a controlled environment before it reaches your infrastructure.
Protocol Deep Dive - Attacks & Technical Details
NetSim Cyber performs field-level rewrites - not generic packet fuzzing. Each protocol has attack modules that parse protocol structure, field semantics, and checksum requirements.
Synchrophasor | IEEE C37.118
The standard for synchrophasor data transmission in Wide Area Monitoring Systems (WAMS). Used for real-time grid monitoring, state estimation, and protection. Supports 2005 (v1), 2011 (v2), and 2024 profiles including the 64-phasor, 4-frequency-channel model.

| Attacks | Technical Details |
|---|---|
|
|
GOOSE / SV | IEC 61850
Generic Object-Oriented Substation Events (GOOSE) and Sampled Values (SV) carry substation communication in IEC 61850 networks. Attacks on these protocols can trigger false breaker trips, corrupt protection relay logic, and disrupt substation automation.
| Attacks | Technical Details |
|---|---|
|
|
Modbus TCP
A common protocol in industrial control systems and SCADA environments. Register tampering and coil manipulation can cause incorrect actuator commands and corrupt historian data without raising alarms.
| Attacks | Technical Details |
|---|---|
|
|
DNP3 | IEEE 1815
The standard protocol for utility-to-substation communication in North America. Unauthorized control commands and replay attacks can trigger remote switching operations and corrupt SCADA historian records.
| Attacks | Technical Details |
|---|---|
|
|
Integration with Industry-Standard Power System Simulators
NetSim Cyber interfaces with real-time power system simulators and electrical platforms listed below.
Why NetSim Cyber?
| Feature | Description |
|---|---|
| Post-Exploitation Focus | Evaluates grid impact after a breach - not how it occurred. No pen-testing, no malware deployment. Controlled lab environment only. |
| Protocol-Aware Mutation | Field-level rewrites on Synchrophasor, GOOSE, Modbus & DNP3 - not generic packet fuzzing. |
| Wire-Valid Packets | CRCs & transport checksums recalculated post-mutation - modified packets remain indistinguishable on the wire. |
| Software Digital Twin | Hardware testbeds are costly, inflexible, hard to scale. NetSim Cyber functions as a digital twin - safe, scalable, zero hardware risk. |
| Power System Integrations | Direct interfaces with OPAL-RT, RTDS, HYPERSIM, PSCAD, MATLAB/Simulink, Typhoon HIL, OpenPMU & openPDC. |
| Proactive Resilience | Validate detection and countermeasures before attacks occur on live infrastructure |
Who Is NetSim Cyber For?
Protocol Support Status & Roadmap
NetSim Cyber supports attack simulation across IEEE C37.118 Synchrophasor, IEC 61850 GOOSE/SV, Modbus TCP, and DNP3 (IEEE 1815).
Currently under active development:Publications that have used NetSim
- Supervised ML framework for DOS Attack Detection and Mitigation for Synchrophasor data transmitted from PMU to PDC (https://ieeexplore.ieee.org/document/11162614)
- A Method for Achieving Confidentiality and Integrity in IEC 61850 GOOSE Messages (https://ieeexplore.ieee.org/document/9079598)
- Optimal Energy Routing in Microgrids with IEC61850 based Energy Routers (https://ieeexplore.ieee.org/document/8764599)
- On IEC 61850 communication networks in smart grid, methodology of implementation and performance analysis on a experimental platform (https://ieeexplore.ieee.org/document/8585706)
- Testing of IEC 61850 System Solutions (https://ieeexplore.ieee.org/document/9429718)
- Performance Analysis of IEC 61850 Messages in LTE Communication for Reactive Power Management in Microgrids ( https://www.mdpi.com/1996-1073/13/22/6011)
- Performance Analysis of Smart Grid Communication Networks Using Co-Simulation ( https://ieeexplore.ieee.org/document/10735155)
- Communication Assisted Protection Scheme Based on Artificial Neural Networks for Multi-Microgrid ( https://ieeexplore.ieee.org/document/10387437)
- Cyber Resilient 5G Enabled Communication Framework for Virtual Power Systems ( https://ieeexplore.ieee.org/document/11135712)





